Open Source SSO (Single-Sign On)
Enable users to sign up with their existing social or enterprise identity providers.
What is SSO (Single-Sign On)?
A user creates an account with an identity provider - such as Google, Facebook or Okta. With SSO or Single Sign On, the user can authenticate themselves into any other application based on their information with the identity provider (”Sign in with Google”)
Similar to how a government issues IDs which are accepted by other entities such as banks and airports, identity providers (eg: Google) verify user information for other entities such as SaaS applications.
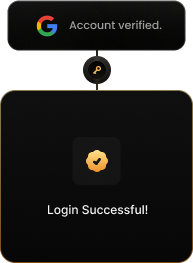
User Flow
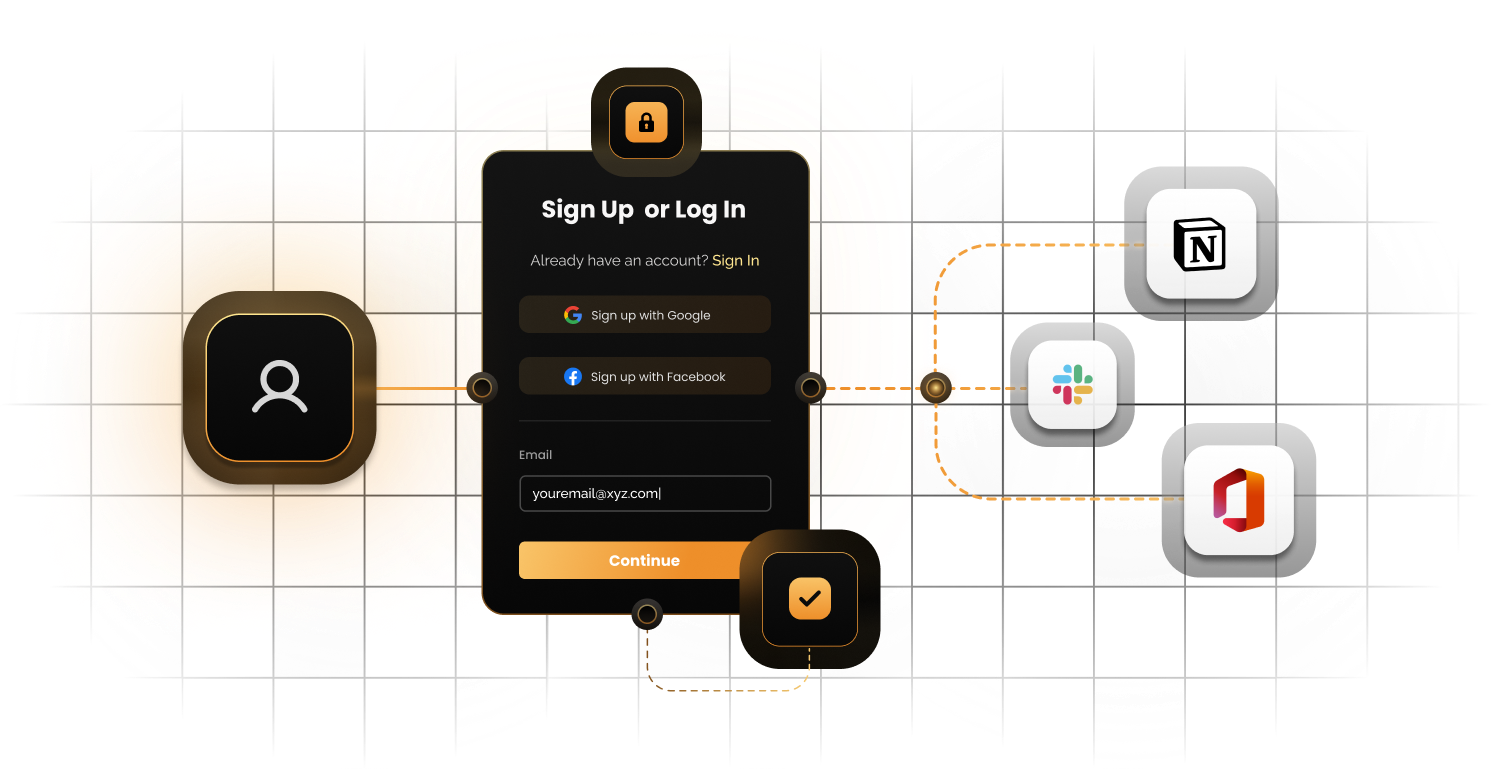
1
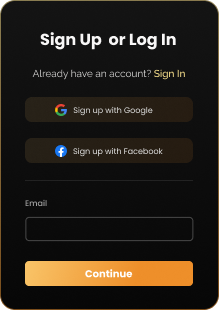
The user lands on the sign-in screen with SSO buttons such as "Sign in with Google"
2
The user clicks an SSO button and is redirected to the identity provider (such as Google)
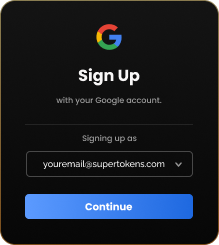
3
Google authenticates the user and passes an auth code token back. The application stores the token and grants access to the user.
4
The application can also use the auth token to ask Google for information about the user. This can range from name, email ID, to more specific information that the user has shared with the identity provider.
Social vs Enterprise SSO
Social SSO
Reduces user friction
Most often used by individuals, using the product in a personal capacity or as part of small teams / companies.
Enterprise SSO
Ensures robust access control
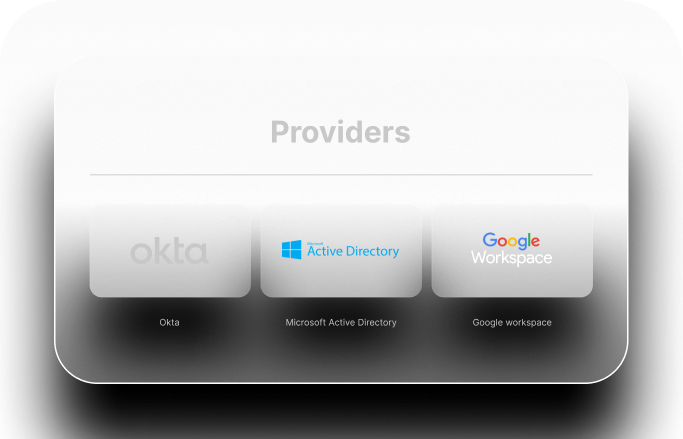
Enterprise companies use identity providers like Okta and Microsoft Active Directory to secure employee access. B2B products have to implement enterprise SSO in order for a buyer's employees to access the service.
Protocols involved
For SSO to work, both the identity provider and service provider have to agree on a standard. Similar to how bartenders can all understand drivers licenses but might not know what to do with birth certificates.
Within SSO, the main standards are OAuth 2.0, SAML, OIDC and LDAP.

Security Assertion Markup Language (SAML)
When the identity provider (Okta) sends a SAML assertion to the service provider (the application), the service provider can be confident of the user's identity. This protocol is more often used by enterprise SSO providers.

Open Authorization (OAuth 2.0 + OIDC)
An identity provider (Google) would return an access and an ID token which a service provider (the application) can use to request resources such as learning about a user's name.

Why use SuperTokens?
SuperTokens Benefits

Implement SSO quickly
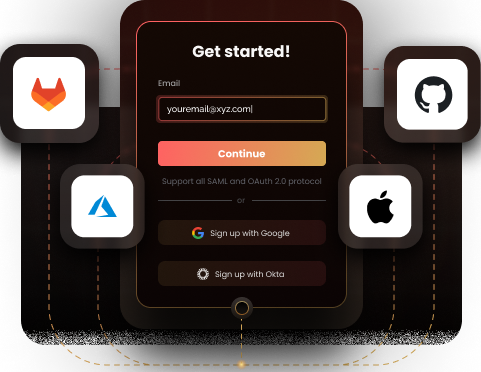
SuperTokens has integrations with the 5 major identity providers by default. However, more powerfully, it allows developers to add ANY SSO provider to their application within an hour - as long as the provider uses the OAuth 2.0 or SAML protocol.


Additional functionality for B2C and B2B Apps
For B2C apps, combine other authentication methods such as passwordless auth, 2FA with fair, flexible pricing. For B2B apps, combine enterprise SSO with multi-tenancy to enable each organization to have its own SSO configuration and user pools


Open Source and self-hosting
Self-hosting with SuperTokens is free. Our core project has ~10,000 stars on Github and we're trusted by startups and large enterprises alike


Start Today
Try supertokens to implement SSO authentication. - we make it easy!
Looking to implement SSO authentication on your own?